25 September 2023
Impulse Offer
A new law is a big deal…
Cybersecurity is a big deal too…
So the Cyber Resilience Act really is a very big deal…
That’s why we have also decided to make a big deal of this new regulation affecting cybersecurity. More specifically, we want to shed light on what is going to change for manufacturers in light of the Cyber Resilience Act.
What is the context behind the Cyber Resilience Act?
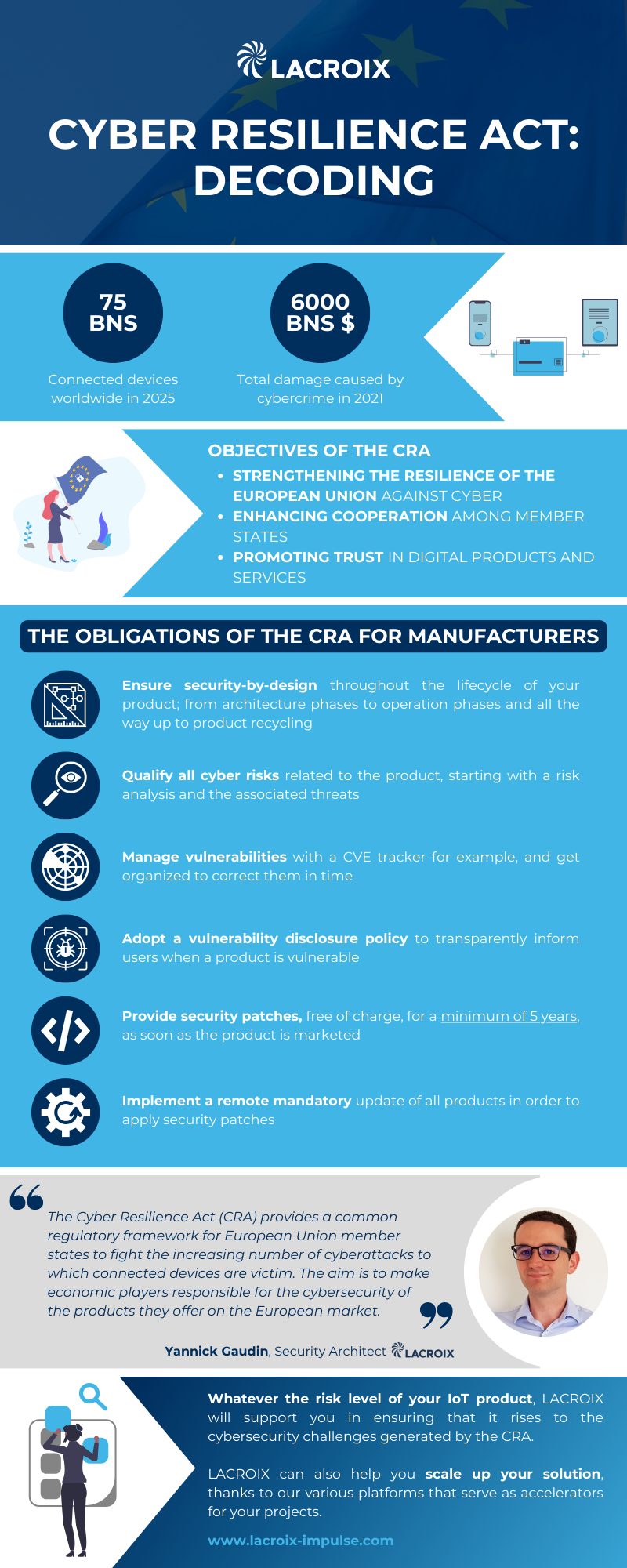
Studies show that the number of connected objects has increased exponentially over recent years. Today, there are 20 billion of them. In 2025, over 75 billion connected objects will be deployed worldwide. It makes your head spin doesn’t it?
At the same time, cyber-attacks are becoming more frequent… as are their “successes” which generate considerable financial costs (after all, we’re talking about 5.5 billion euros!) and fuel an entire ecosystem around cybercrime.
In this context, the European Commission has decided to take action by proposing a legislative act to reinforce the safety of IoT objects. Often seen as a constraint, the arrival of a new regulation nevertheless offers a great opportunity for everyone to improve their cyber environment.
And the Cyber Resilience Act is not alone, it is the latest successor in a line of cyber standards (ISO 270001, FIPS 140, IEC 62443, EN 303645) and regular standards (CE, RoHS and Radio Equipment Directive, ANSSI qualification, GDPR compliance, USA Patriot Act). Other standards are expected in the near future, such as the RED cyber extension for all new products in 2024.
What are the obligations of the Cyber Resilience Act for manufacturers?
The CRA brings together a set of obligations for IoT manufacturers (physical products, cloud and servers):
However, it’s not rocket science if you’re well supported…
- Ensure security-by-designthroughout the lifecycle of your product; from architecture phases to operation phases and all the way up to product recycling
- Qualify all cyber risks related to the product, starting with a risk analysis and the associated threats
- Manage vulnerabilities with a CVE tracker for example, and get organized to correct them in time
- Adopt a vulnerability disclosure policy to transparently inform users when a product is vulnerable
- Provide security patches, free of charge, for a minimum of 5 years, as soon as the product is marketed
- Implement a remote mandatory update of all products in order to apply security patches
As you will have understood, the CRA is no small matter and this new cybersecurity regulation requires certain changes to be made in order to comply with and meet the standards required. The question is not whether your system will be attacked, but when, and what the impacts will be, so it’s better to be ready for it!
 If you are interested in the CRA, we invite you to watch our PizzaIoT #2 conference “The Cybersecurity Act, what impacts will it have on my IoT project?”. The good news is that you can replay the video.
If you are interested in the CRA, we invite you to watch our PizzaIoT #2 conference “The Cybersecurity Act, what impacts will it have on my IoT project?”. The good news is that you can replay the video.